Why NoSQL injection happens in MongoDB
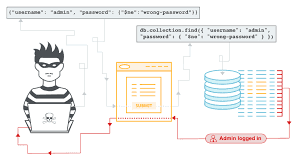
When a backend receives login data (for example, an email and password), it usually queries MongoDB to find a matching user.
The main problem appears when the backend uses user input directly in a MongoDB query (for example, using req.body without validation).
The main culprit
MongoDB queries are not limited to “exact match” lookups. MongoDB supports query operators (like $ne, $gt, $regex) to enable powerful searching.
If an attacker can send an object that contains these operators, and the backend passes that object directly into the query, MongoDB may execute those operators as part of the query, instead of treating the input as plain text.
Why this matters
MongoDB is designed to be flexible and powerful, which is useful in real applications. But without strict input validation and safe query building, that same flexibility can be abused to bypass authentication or access data in unintended ways.